The Power of Wide OSINT Analysis
by Cognyte
The Power of Wide OSINT Analysis
From Web-Centric to Multi-Source Intelligence
- Executive Summary
- The Value of OSINT
- Limits of Traditional WEBINT
- Who Benefits from Wide OSINT
- When SIGINT Falls Short
- Applying Wide OSINT
- Conclusion
Executive Summary
Intelligence analysts today face escalating threats that cut across borders and networks. Critical indicators of illicit activity, including terrorism, organized crime, financial crime and cybercrime, often surface in open data sources first, making open-source intelligence (OSINT) a critical discipline for national security organizations, law enforcement agencies and other government authorities.
Massive volumes of data relevant to intelligence analysis and investigations are available, from government reports to satellite feeds. Yet too many organizations remain stuck in a traditional web intelligence (WEBINT) mindset, relying almost exclusively on information analysis obtained on social media and messaging platforms. This narrow approach overwhelms analysts with noise while leaving critical blind spots.
To keep pace with widening threats, agencies need to adopt a Wide OSINT approach, which extends to include the analysis of Publicly Available Information (PAI) and Commercially Available Information (CAI), such as government records, commercial datasets, geospatial feeds and more.
Cognyte's Wide OSINT analysis framework is a practical guide that helps intelligence and law enforcement agencies effectively deploy the Wide OSINT approach. It maps the key steps required to generate meaningful intelligence faster. Supported by modern decision intelligence platforms, these steps are implemented within a unified system, enabling analysts to conduct both targeted investigations and strategic analysis designed to uncover trends, patterns and anomalies that would otherwise remain hidden. When Wide OSINT analysis is combined with additional intelligence sources, such as SIGINT, agencies unlock new domains of insight and a deeper understanding of complex threats.
Read on to explore the framework in detail and understand how its components work.
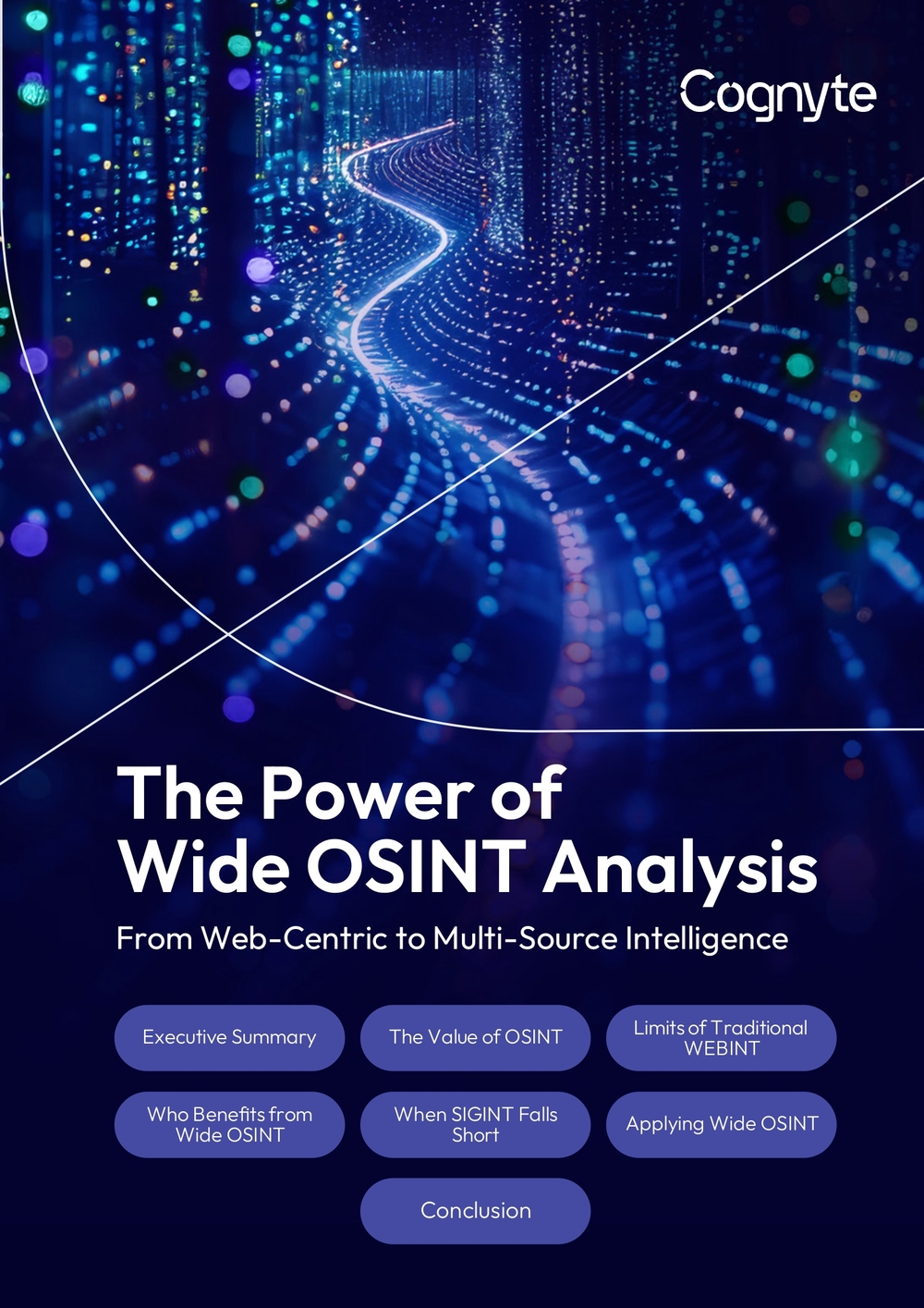
Cognyte's Wide OSINT Framework (High-Level View)
- Data Sources
- Technology Capabilities
- Analytical Methodologies
- Organizational Structure
Value gained
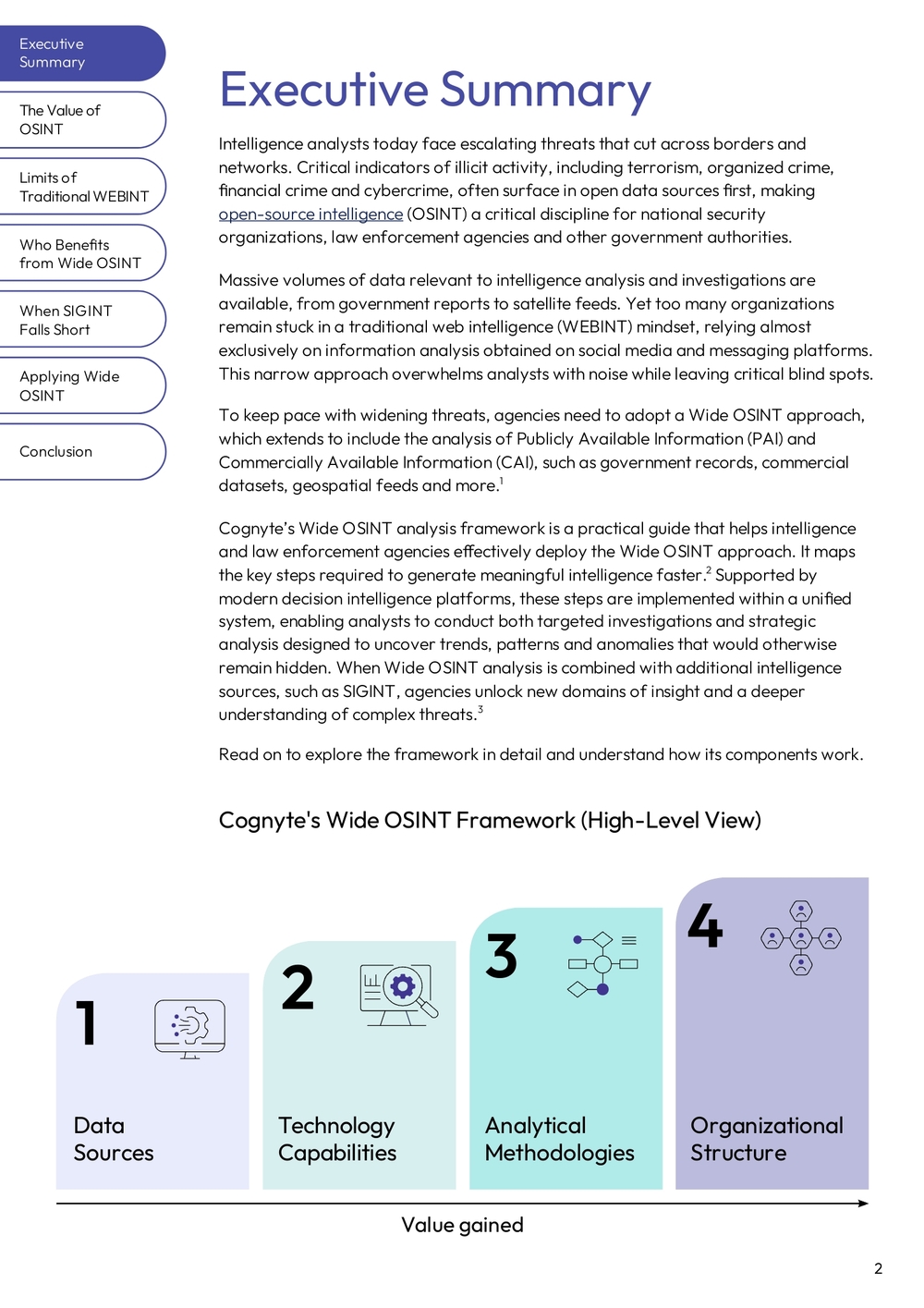
The Value of OSINT
Open-source Intelligence (OSINT) is the process of gathering, analyzing and transforming publicly available information into actionable insights that help law enforcement, intelligence and military agencies detect, investigate and prevent threats.
Unlike classified sources, OSINT relies on open data, such as:
- Social media and group messaging platforms (X, Telegram, Discord, TikTok, Weibo, WeChat)
- Commercial databases (Moody's, LexisNexis)
- Publicly accessible intelligence databases and watchlists (OpenSanctions, Interpol Red Notices)
- AIS and shipping data
- News articles and media reports
- Public records (court filings, property records, business registrations)
- Satellite imagery (publicly accessible or commercially available sources)
- Government publications and white papers
- Academic research
OSINT has become a cornerstone of modern investigations. It complements classified intelligence sources by providing scalable and often real-time visibility into local, national and international activity. However, as the volume and variety of public data grows, many organizations still approach OSINT narrowly, relying on WEBINT that is usually applied on a target-by-target basis and focused on social media and web content, while missing broader insights available across other open data sources.
Limits of Traditional WEBINT
The traditional WEBINT approach enables teams to analyze data from social media, the web and messaging platforms. While this can provide valuable intelligence insights, many security organizations are finding that it's no longer enough in today's complex environment, due to limitations that include:
Tunnel vision
WEBINT relies mainly on analyzing data from social media, the web and messaging platforms, causing agencies to miss signals found in financial, regulatory, media and geospatial data.
Volume over value
Success is often measured by how much data is gathered, not by what is learned, with analysts spending hours sifting through irrelevant posts.
Wide OSINT reverses that logic: start with the investigative or intelligence question, then gather and analyze only data that is relevant.
Analytical capabilities including entity resolution, link analysis and anomaly detection are leveraged to extract insights from the data, uncovering hidden patterns and insights.
Tactical vs. strategic scope
A WEBINT-only approach works well for tightly defined, short-term investigative tasks, like verifying online aliases or tracing a suspect's last message but falls short on strategic analysis. Wide OSINT can support both tactical investigations as well as long-range intelligence. Wide OSINT can better support strategic and complex investigations, including connecting online personas to their real-world identities, activities and assets.
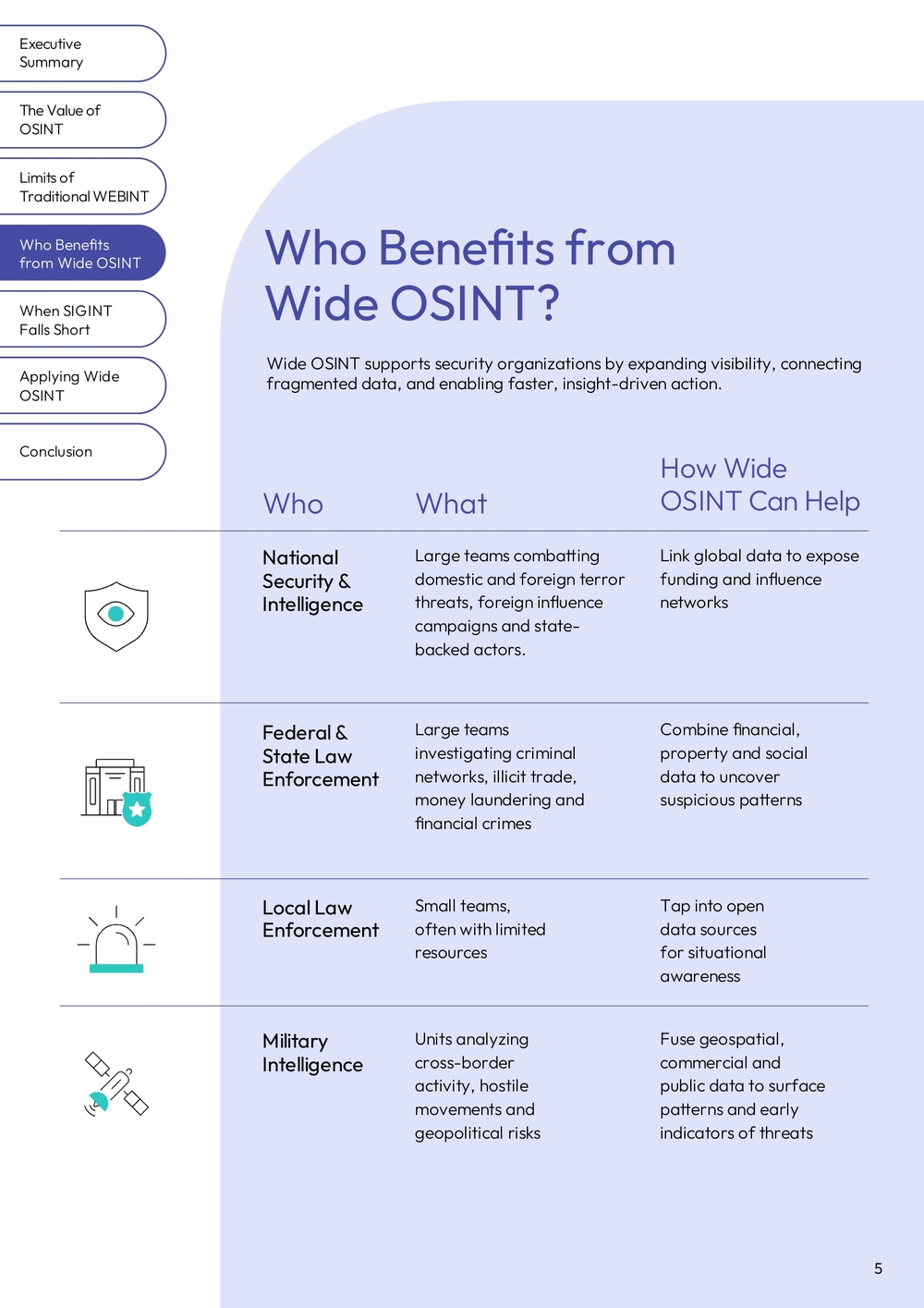
Who Benefits from Wide OSINT?
Wide OSINT supports security organizations by expanding visibility, connecting fragmented data, and enabling faster, insight-driven action.
| Who | What | How Wide OSINT Can Help |
|---|---|---|
| National Security & Intelligence | Large teams combatting domestic and foreign terror threats, foreign influence campaigns and state-backed actors. | Link global data to expose funding and influence networks |
| Federal & State Law Enforcement | Large teams investigating criminal networks, illicit trade, money laundering and financial crimes | Combine financial, property and social data to uncover suspicious patterns |
| Local Law Enforcement | Small teams, often with limited resources | Tap into open data sources for situational awareness |
| Military Intelligence | Units analyzing cross-border activity, hostile movements and geopolitical risks | Fuse geospatial, commercial and public data to surface patterns and early indicators of threats |
When SIGINT Falls Short
For many intelligence and law enforcement agencies, SIGINT remains the cornerstone of investigative and analytical work. However, even the most advanced SIGINT capabilities face capacity limits and constraints, especially in cases of foreign operations. In addition, with most communications data being encrypted today, obtaining intelligence value from SIGINT requires cutting edge network intelligence systems which not every agency has access to. Wide OSINT bridges those blind spots, by connecting online, commercial and geospatial sources.
These examples illustrate high-impact scenarios where Wide OSINT adds strategic value:
Financial crime & sanctions evasion:
Unmask shell-company networks, trace cryptocurrency trails and link ownership across corporate registries.
Public safety:
Fuse social media discourse with geolocation and local news reports to detect early signals of violence or riots.
Foreign influence campaigns:
Analyze disinformation networks by combining social posts with web attribution and network-of-domains mapping.
Illicit trade:
Track anomalous flight/maritime patterns, shipping manifests, customs declarations and procurement contracts to detect smuggling or diversion.

OSINT Success Stories
Recent examples illustrate that when illicit actors span borders or hidden channels, the Wide OSINT approach can provide agencies with the holistic view which SIGINT alone cannot.
Sanctions Evasion
Iran created a covert "ghost fleet" network of oil tankers registered under front companies and sailing under flags of convenience to evade international sanctions.
Vessels turned off their tracking systems (AIS), spoofed identities or transferred oil at sea to hide their movements.
US authorities were able to uncover the fleet's true routes and ownership links by combining open data sources, such as AIS tracking (MarineTraffic), satellite imagery (Planet Labs) and corporate registries, supporting sanctions led by the US Treasury's Office of Foreign Assets Control.
Outcome: Findings led to U.S. sanctions on 17 tankers and 10 companies.
Election Interference
During Poland's 2025 presidential campaign, the national cybersecurity agency (NASK) identified suspicious ads on social media that appeared to support one candidate but were designed to undermine opponents.
Investigators traced the ads to foreign-linked pages and accounts that spent hundreds of thousands of zlotys through opaque funding sources.
Outcome: Using open data sources, including social media records, domain registrations and content provenance checks, analysts uncovered a coordinated disinformation campaign tied to Russian actors.
Human Trafficking Operation
In 2024, INTERPOL and the Organization for Security and Co-operation in Europe (OSCE) coordinated an international operation targeting human trafficking networks that recruit victims online through fake job ads, escort listings and encrypted messaging platforms.
Investigators used open-source intelligence to identify recruiters and victims by analyzing social media, websites and Telegram channels, and then cross-referencing usernames and facial images with INTERPOL and national databases.
Outcome: The effort uncovered 68 potential victims, 146 suspected traffickers, and 162 URLs linked to online recruitment activity across nine countries.
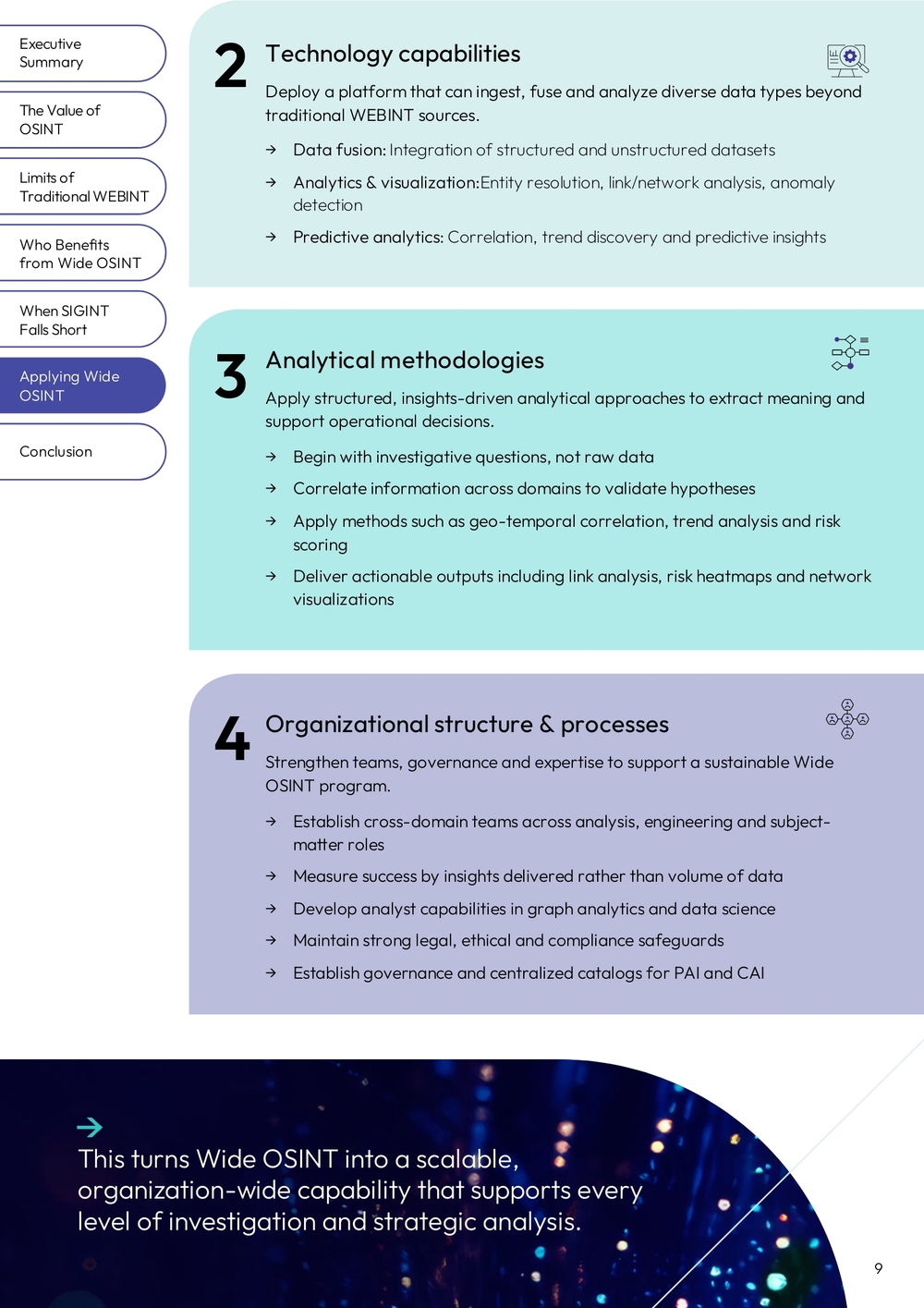
Wide OSINT: A Practical Framework
To put Wide OSINT into practice, agencies need a clear operational framework. Cognyte's Wide OSINT framework focuses on four key areas: data, technology, analytics and organization.
Cognyte's Wide OSINT Framework (Detailed)
1. Data sources
Expand beyond traditional WEBINT sources (social media, dark web, messaging apps) to incorporate diverse datasets that create a broader and richer intelligence picture.
→ PAI: government records, corporate registries, judicial filings, sanctions databases, flight/maritime trackers → CAI: financial databases (Moody's, LexisNexis), high-resolution commercial satellite imagery
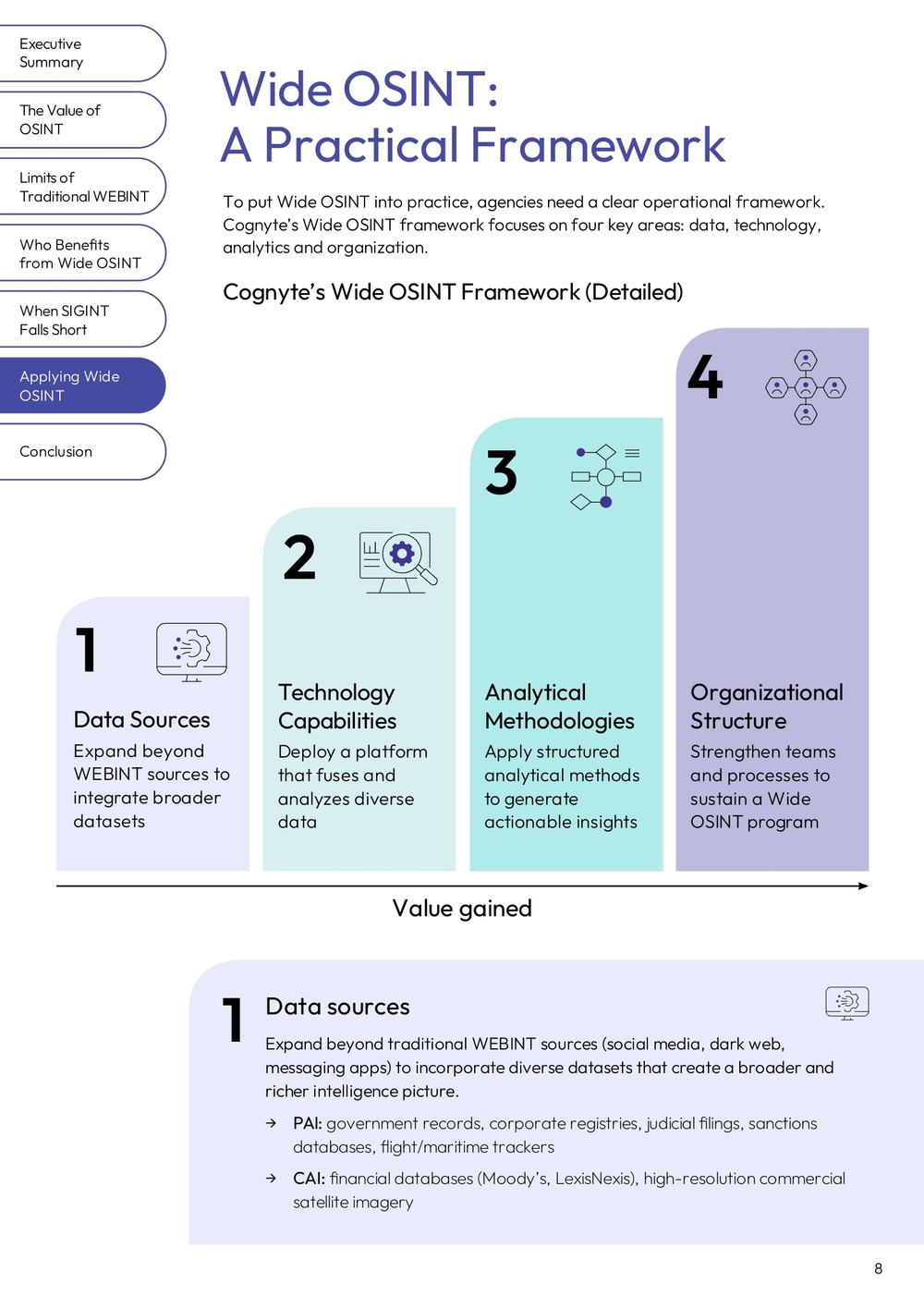
2. Technology capabilities
Deploy a platform that can ingest, fuse and analyze diverse data types beyond traditional WEBINT sources.
→ Data fusion: Integration of structured and unstructured datasets → Analytics & visualization: Entity resolution, link/network analysis, anomaly detection → Predictive analytics: Correlation, trend discovery and predictive insights
3. Analytical methodologies
Apply structured, insights-driven analytical approaches to extract meaning and support operational decisions.
→ Begin with investigative questions, not raw data → Correlate information across domains to validate hypotheses → Apply methods such as geo-temporal correlation, trend analysis and risk scoring → Deliver actionable outputs including link analysis, risk heatmaps and network visualizations
4. Organizational structure & processes
Strengthen teams, governance and expertise to support a sustainable Wide OSINT program.
→ Establish cross-domain teams across analysis, engineering and subject-matter roles → Measure success by insights delivered rather than volume of data → Develop analyst capabilities in graph analytics and data science → Maintain strong legal, ethical and compliance safeguards → Establish governance and centralized catalogs for PAI and CAI
This turns Wide OSINT into a scalable, organization-wide capability that supports every level of investigation and strategic analysis.
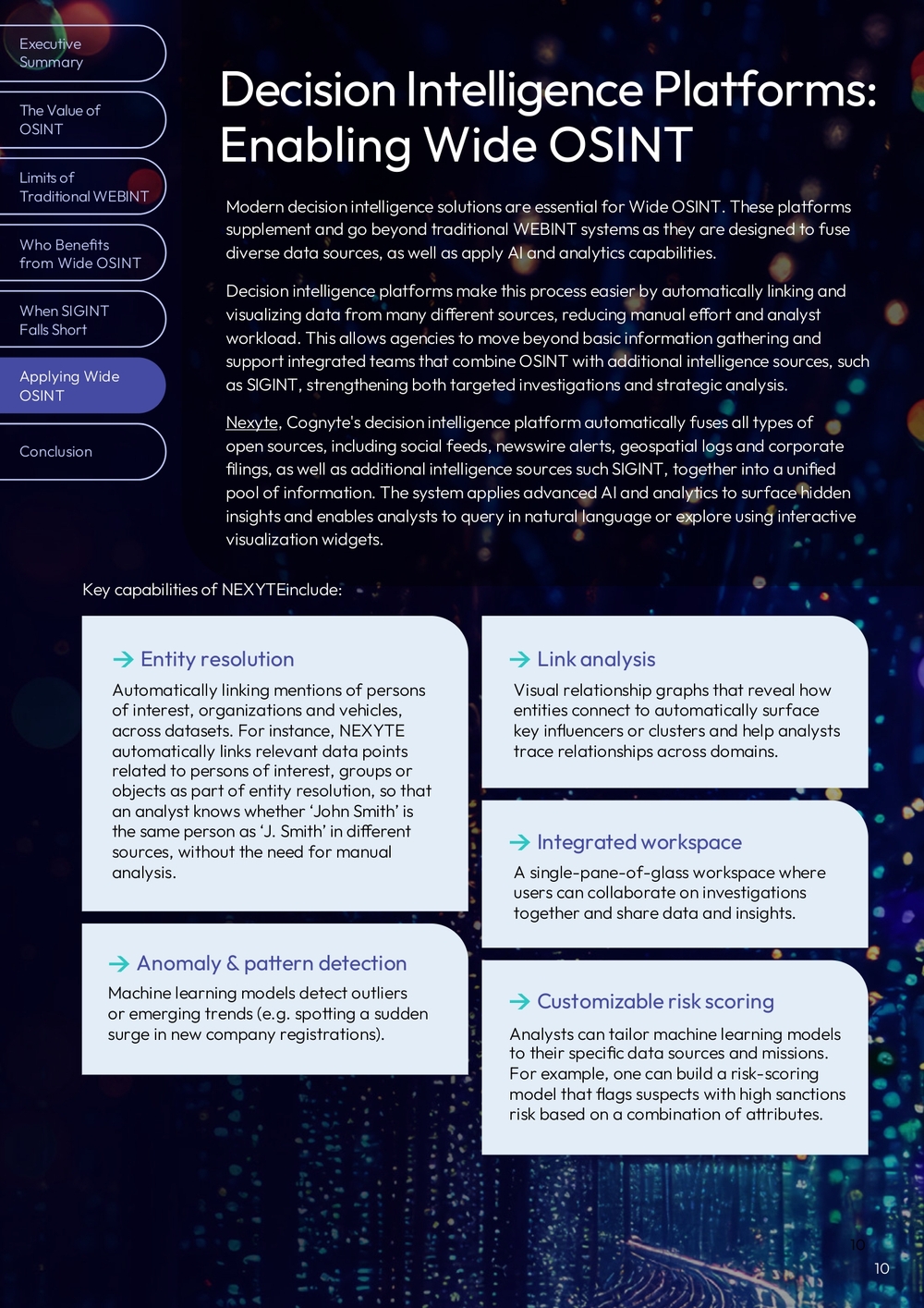
Decision Intelligence Platforms: Enabling Wide OSINT
Modern decision intelligence solutions are essential for Wide OSINT. These platforms supplement and go beyond traditional WEBINT systems as they are designed to fuse diverse data sources, as well as apply AI and analytics capabilities.
Decision intelligence platforms make this process easier by automatically linking and visualizing data from many different sources, reducing manual effort and analyst workload. This allows agencies to move beyond basic information gathering and support integrated teams that combine OSINT with additional intelligence sources, such as SIGINT, strengthening both targeted investigations and strategic analysis.
Nexyte, Cognyte's decision intelligence platform automatically fuses all types of open sources, including social feeds, newswire alerts, geospatial logs and corporate filings, as well as additional intelligence sources such SIGINT, together into a unified pool of information. The system applies advanced AI and analytics to surface hidden insights and enables analysts to query in natural language or explore using interactive visualization widgets.
Key capabilities of NEXYTE include:
Entity resolution
Automatically linking mentions of persons of interest, organizations and vehicles, across datasets. For instance, NEXYTE automatically links relevant data points related to persons of interest, groups or objects as part of entity resolution, so that an analyst knows whether 'John Smith' is the same person as 'J. Smith' in different sources, without the need for manual analysis.
Anomaly & pattern detection
Machine learning models detect outliers or emerging trends (e.g. spotting a sudden surge in new company registrations).
Link analysis
Visual relationship graphs that reveal how entities connect to automatically surface key influencers or clusters and help analysts trace relationships across domains.
Integrated workspace
A single-pane-of-glass workspace where users can collaborate on investigations together and share data and insights.
Customizable risk scoring
Analysts can tailor machine learning models to their specific data sources and missions. For example, one can build a risk-scoring model that flags suspects with high sanctions risk based on a combination of attributes.
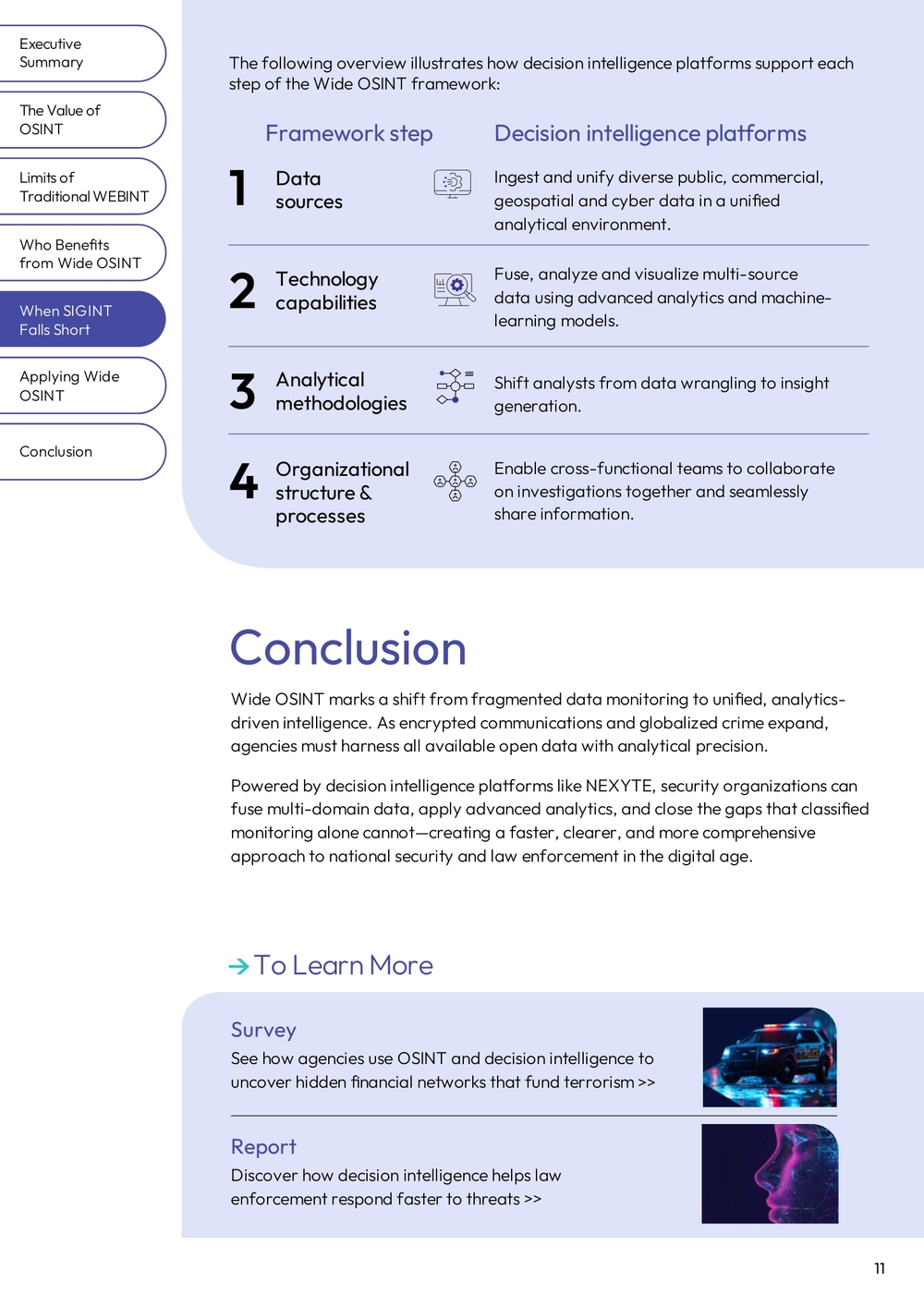
Framework step Decision intelligence platforms
1. Data sources
Ingest and unify diverse public, commercial, geospatial and cyber data in a unified analytical environment.
2. Technology capabilities
Fuse, analyze and visualize multi-source data using advanced analytics and machine-learning models.
3. Analytical methodologies
Shift analysts from data wrangling to insight generation.
4. Organizational structure & processes
Enable cross-functional teams to collaborate on investigations together and seamlessly share information.
Conclusion
Wide OSINT marks a shift from fragmented data monitoring to unified, analytics-driven intelligence. As encrypted communications and globalized crime expand, agencies must harness all available open data with analytical precision.
Powered by decision intelligence platforms like NEXYTE, security organizations can fuse multi-domain data, apply advanced analytics, and close the gaps that classified monitoring alone cannot—creating a faster, clearer, and more comprehensive approach to national security and law enforcement in the digital age.
To Learn More
Survey
See how agencies use OSINT and decision intelligence to uncover hidden financial networks that fund terrorism >>
Report
Discover how decision intelligence helps law enforcement respond faster to threats >>
About Cognyte
Cognyte, a global leader in data processing and investigative analytics solutions, helps government agencies and other organizations eliminate the unknown and make smarter, faster decisions with Actionable Intelligence for a Safer World™.
Notes
- https://www.dni.gov/files/ODNI/documents/IC_OSINT_Strategy.pdf
- https://www.police1.com/spotlight-how-cognytes-nexyte-decision-intelligence-platform-allows-pds-to-allocate-resources
- https://www.police1.com/police-products/investigation/Investigative-Software/decision-intelligence-can-transform-how-law-enforcement-officers-work-with-digital-forensics
- https://www.wcoomd.org/-/media/wco/public/global/pdf/topics/enforcement-and-compliance/activities-and-programmes/security-programme/osint-report_final.pdf
- https://maritime-executive.com/article/u-s-targets-iran-s-ghost-fleet-sanctioning-17-tankers-and-10-operators
- https://www.reuters.com/world/europe/poland-uncovers-what-it-says-may-be-foreign-funded-election-interference-2025-05-14/#:~:text=,research%20institute%20dealing%20with%20cybersecurity
- https://www.interpol.int/en/News-and-Events/News/2024/Cyber-enabled-human-trafficking-coordinated-action-targets-online-recruitment-and-exploitation
- https://www.osce.org/sites/default/files/f/documents/8/d/579190_0.pdf