2026 Border & Maritime Intel: Top 5 Challenges
by Cognyte
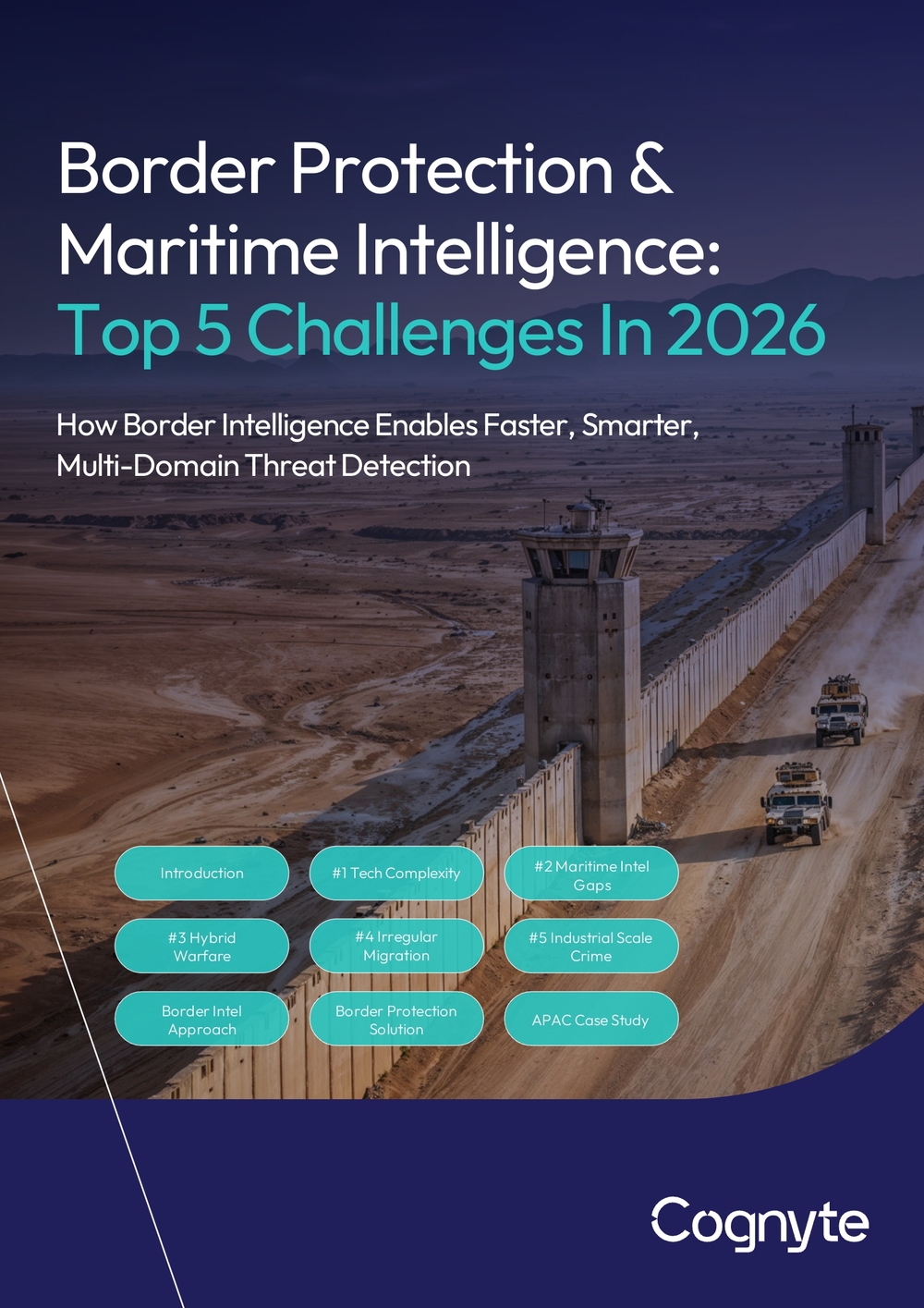
Border Protection & Maritime Intelligence:
Top 5 Challenges In 2026
How Border Intelligence Enables Faster, Smarter, Multi-Domain Threat Detection
Introduction
The New Border Reality
Borders worldwide are becoming multidomain frontlines where geopolitical rivalries, hybrid warfare and transnational crime unfold across physical and digital domains. Modern border protection is no longer only about keeping military threats and criminals out, it's about understanding what's coming in, what's moving across and what's hidden beneath.
Threats no longer move in linear, predictable ways. They exploit:
- Land borders
- Maritime routes
- Airspace
- Cyber infrastructure
- Information ecosystems
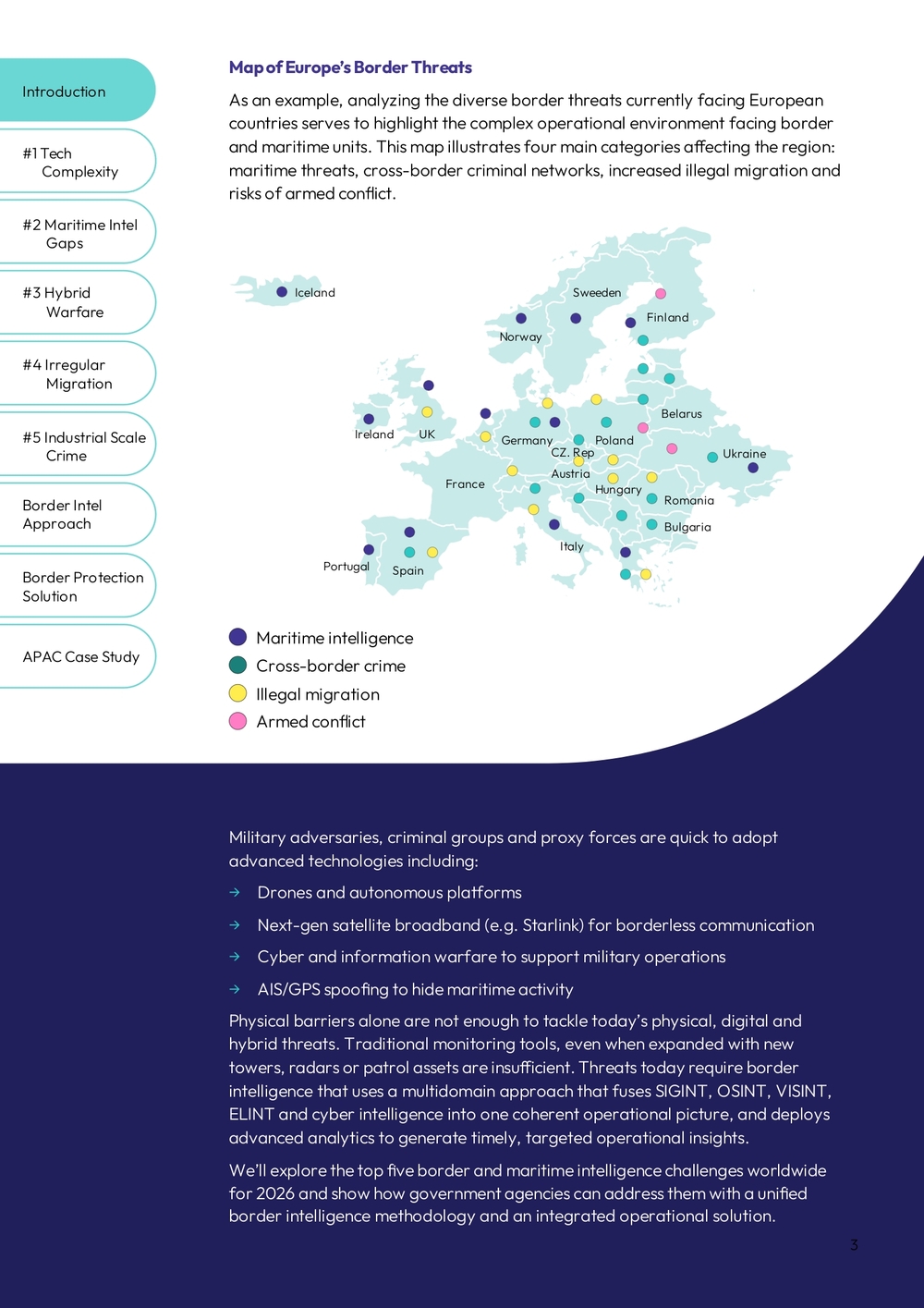
Map of Europe's Border Threats
As an example, analyzing the diverse border threats currently facing European countries serves to highlight the complex operational environment facing border and maritime units. This map illustrates four main categories affecting the region: maritime threats, cross-border criminal networks, increased illegal migration and risks of armed conflict.
Military adversaries, criminal groups and proxy forces are quick to adopt advanced technologies including:
→ Drones and autonomous platforms → Next-gen satellite broadband (e.g. Starlink) for borderless communication → Cyber and information warfare to support military operations → AIS/GPS spoofing to hide maritime activity
Physical barriers alone are not enough to tackle today's physical, digital and hybrid threats. Traditional monitoring tools, even when expanded with new towers, radars or patrol assets are insufficient. Threats today require border intelligence that uses a multidomain approach that fuses SIGINT, OSINT, VISINT, ELINT and cyber intelligence into one coherent operational picture, and deploys advanced analytics to generate timely, targeted operational insights.
We'll explore the top five border and maritime intelligence challenges worldwide for 2026 and show how government agencies can address them with a unified border intelligence methodology and an integrated operational solution.
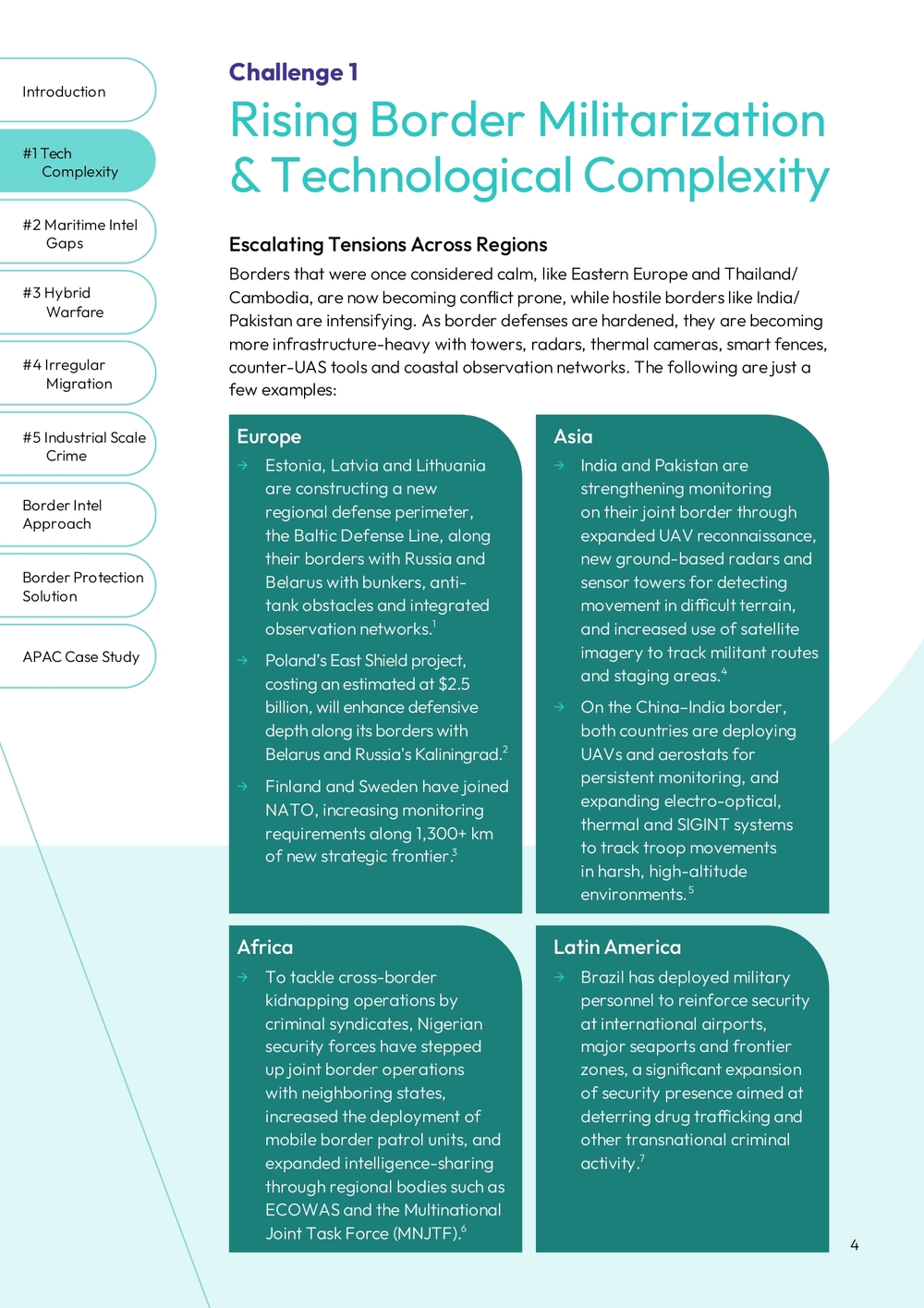
Challenge 1
Rising Border Militarization & Technological Complexity
Escalating Tensions Across Regions
Borders that were once considered calm, like Eastern Europe and Thailand/Cambodia, are now becoming conflict prone, while hostile borders like India/Pakistan are intensifying. As border defenses are hardened, they are becoming more infrastructure-heavy with towers, radars, thermal cameras, smart fences, counter-UAS tools and coastal observation networks. The following are just a few examples:
Europe
→ Estonia, Latvia and Lithuania are constructing a new regional defense perimeter, the Baltic Defense Line, along their borders with Russia and Belarus with bunkers, anti-tank obstacles and integrated observation networks. → Poland's East Shield project, costing an estimated at $2.5 billion, will enhance defensive depth along its borders with Belarus and Russia's Kaliningrad. → Finland and Sweden have joined NATO, increasing monitoring requirements along 1,300+ km of new strategic frontier.
Asia
→ India and Pakistan are strengthening monitoring on their joint border through expanded UAV reconnaissance, new ground-based radars and sensor towers for detecting movement in difficult terrain, and increased use of satellite imagery to track militant routes and staging areas. → On the China–India border, both countries are deploying UAVs and aerostats for persistent monitoring, and expanding electro-optical, thermal and SIGINT systems to track troop movements in harsh, high-altitude environments.
Africa
→ To tackle cross-border kidnapping operations by criminal syndicates, Nigerian security forces have stepped up joint border operations with neighboring states, increased the deployment of mobile border patrol units, and expanded intelligence-sharing through regional bodies such as ECOWAS and the Multinational Joint Task Force (MNJTF).
Latin America
→ Brazil has deployed military personnel to reinforce security at international airports, major seaports and frontier zones, a significant expansion of security presence aimed at deterring drug trafficking and other transnational criminal activity.
Key Takeaways: Many Sensors, Not Enough Intelligence
Modern border environments are becoming more infrastructure-heavy, but two core intelligence challenges persist:
Fragmented View
Radar, cameras, satellite imagery and ground sensors provide critical information from the field. Additional sources such as SIGINT, satellite signals, OSINT and ADINT (Advertising Intelligence, which extracts insights from digital ad-tech data such as device behavior, location patterns and online identifiers) can extend detection far beyond the border strip. Yet each system operates in a silo, limiting holistic situational awareness. A border intelligence approach enables breaking the silos in order to enable borderless awareness and earlier detection of emerging threats.
Short-Term Perspective
Many border units still lack the ability to detect long-term patterns, identify evolving threat behaviors, and prioritize Areas of Interest (AOI) for monitoring. Without advanced analytics capabilities, agencies remain reactive. A border intelligence approach is essential to move from short-term monitoring to proactive, preventive insight and action.
Challenge 2
Gaps In Maritime Intelligence Are Riskier Than Ever
A Perfect Operating Space for Illicit Actors
The vast scale of coastlines and maritime waters gives hostile actors and criminal networks a built-in advantage: it is difficult to monitor and easy to exploit. Especially considering the rising waves of immigration that are increasingly spilling into the maritime domain, where smugglers move people across long, lightly monitored sea routes. Even with coastal radar, AIS monitoring, patrol vessels and satellite imagery, coverage is patchy especially beyond territorial waters, at night, or in poor weather. This creates windows of opportunity that adversaries exploit for malicious activities, including:
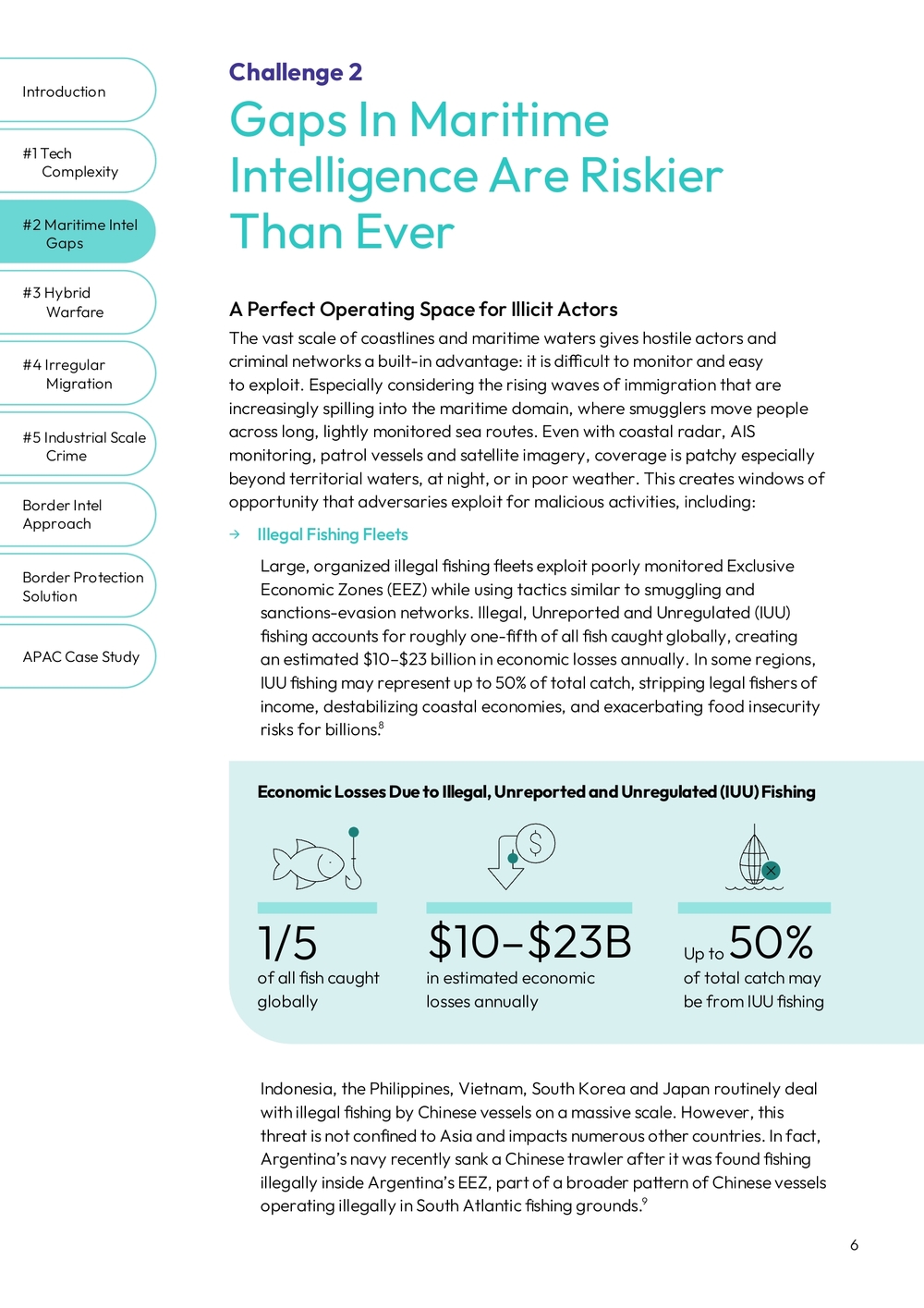
→ Illegal Fishing Fleets Large, organized illegal fishing fleets exploit poorly monitored Exclusive Economic Zones (EEZ) while using tactics similar to smuggling and sanctions-evasion networks. Illegal, Unreported and Unregulated (IUU) fishing accounts for roughly one-fifth of all fish caught globally, creating an estimated $10–$23 billion in economic losses annually. In some regions, IUU fishing may represent up to 50% of total catch, stripping legal fishers of income, destabilizing coastal economies, and exacerbating food insecurity risks for billions.
Economic Losses Due to Illegal, Unreported and Unregulated (IUU) Fishing
- 1/5 of all fish caught globally
- $10–$23B in estimated economic losses annually
- Up to 50% of total catch may be from IUU fishing
Indonesia, the Philippines, Vietnam, South Korea and Japan routinely deal with illegal fishing by Chinese vessels on a massive scale. However, this threat is not confined to Asia and impacts numerous other countries. In fact, Argentina's navy recently sank a Chinese trawler after it was found fishing illegally inside Argentina's EEZ, part of a broader pattern of Chinese vessels operating illegally in South Atlantic fishing grounds.
→ Sanction Evasion and Smuggling Sanction evaders and smugglers routinely deploy "dark" or "ghost" ships vessels that switch off AIS spoofing (Automatic Identification System), falsify identities, spoof GPS positions or change flags mid-route to obscure their true origin, destination and intent.
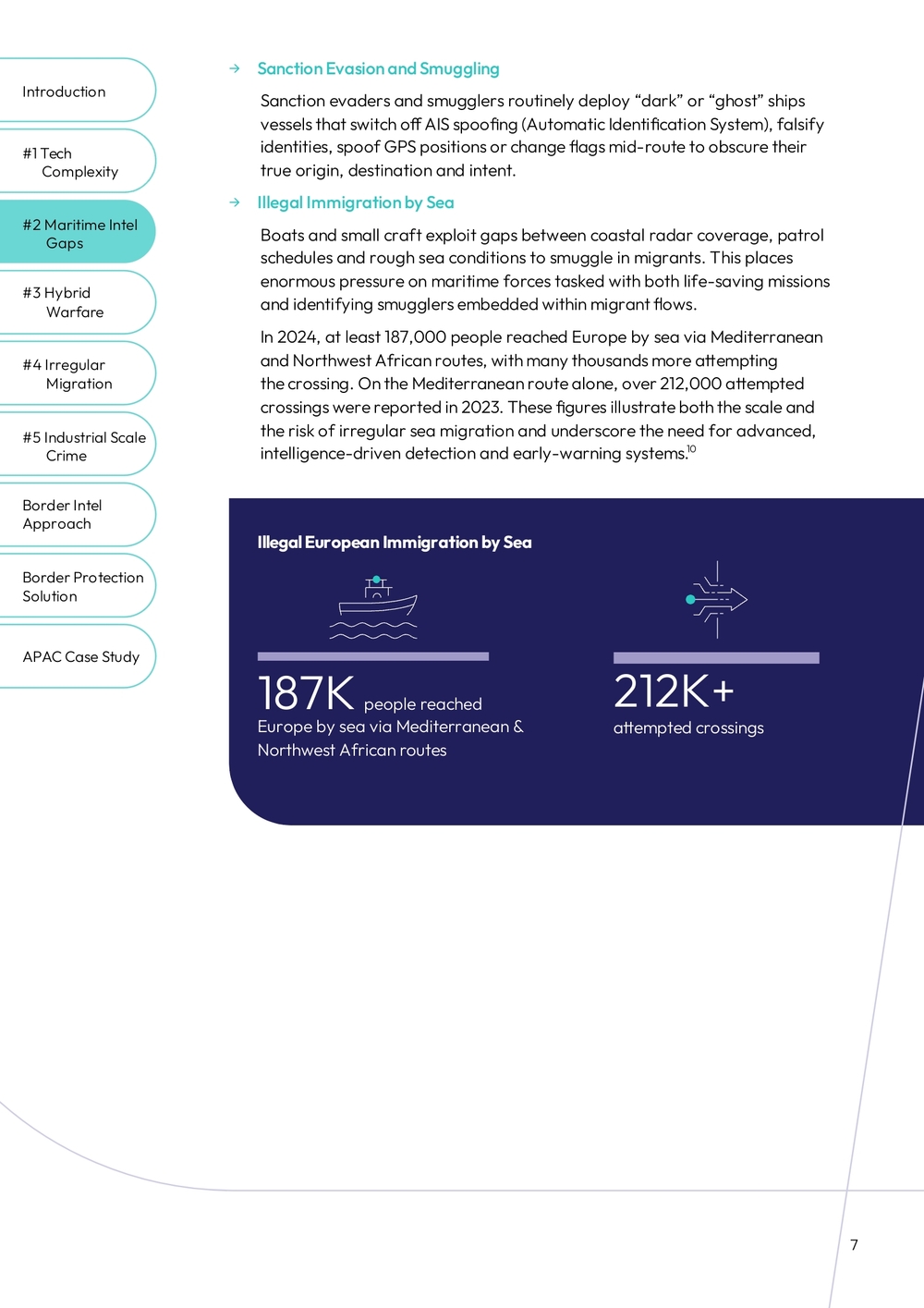
→ Illegal Immigration by Sea Boats and small craft exploit gaps between coastal radar coverage, patrol schedules and rough sea conditions to smuggle in migrants. This places enormous pressure on maritime forces tasked with both life-saving missions and identifying smugglers embedded within migrant flows.
In 2024, at least 187,000 people reached Europe by sea via Mediterranean and Northwest African routes, with many thousands more attempting the crossing. On the Mediterranean route alone, over 212,000 attempted crossings were reported in 2023. These figures illustrate both the scale and the risk of irregular sea migration and underscore the need for advanced, intelligence-driven detection and early-warning systems.
Illegal European Immigration by Sea
- 187K people reached Europe by sea via Mediterranean & Northwest African routes
- 212K+ attempted crossings
How Adversaries Exploit Maritime Gaps
Adversaries are increasingly leveraging technology in their tactics:
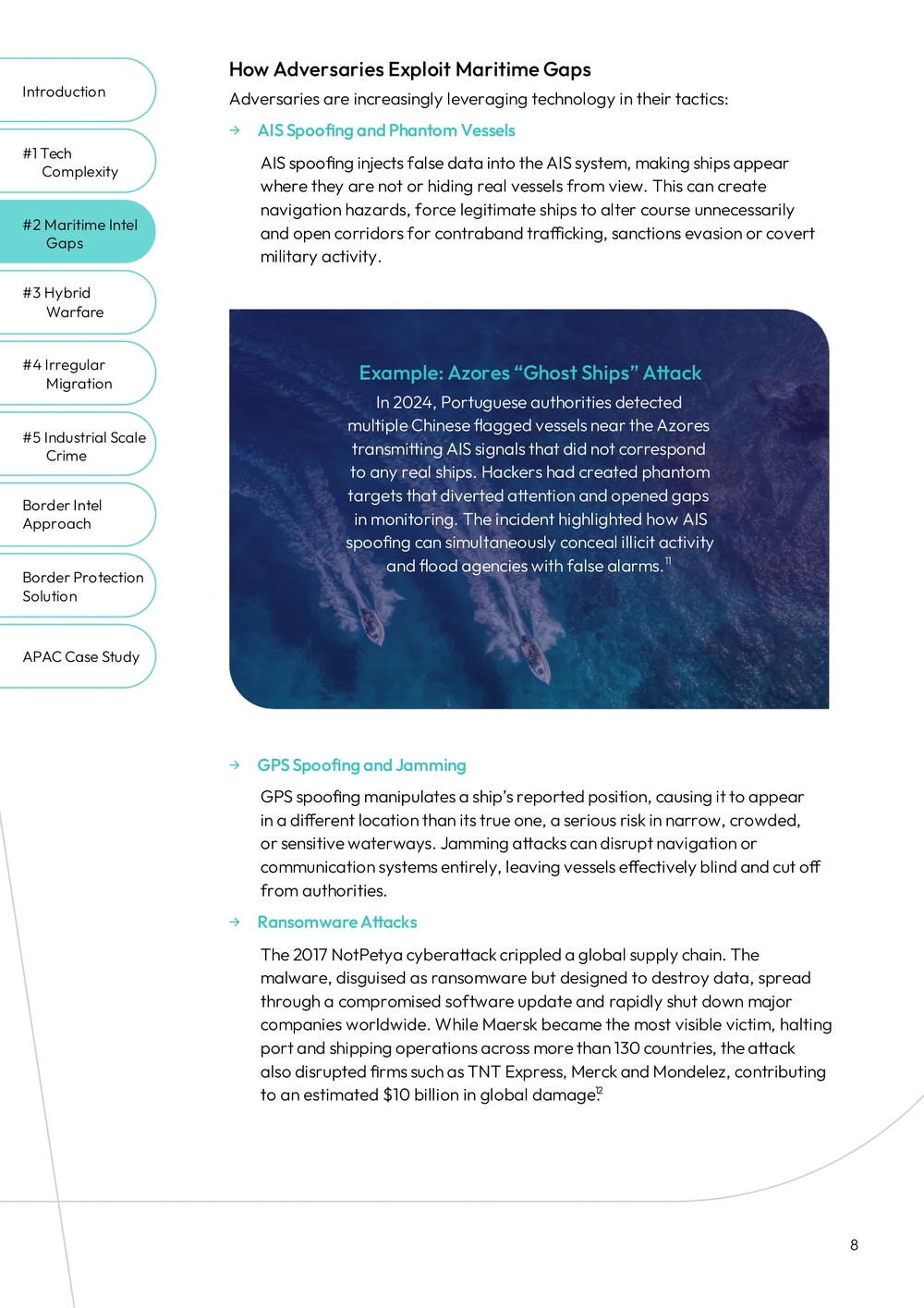
→ AIS Spoofing and Phantom Vessels AIS spoofing injects false data into the AIS system, making ships appear where they are not or hiding real vessels from view. This can create navigation hazards, force legitimate ships to alter course unnecessarily and open corridors for contraband trafficking, sanctions evasion or covert military activity.
Example: Azores "Ghost Ships" Attack
In 2024, Portuguese authorities detected multiple Chinese flagged vessels near the Azores transmitting AIS signals that did not correspond to any real ships. Hackers had created phantom targets that diverted attention and opened gaps in monitoring. The incident highlighted how AIS spoofing can simultaneously conceal illicit activity and flood agencies with false alarms.
→ GPS Spoofing and Jamming GPS spoofing manipulates a ship's reported position, causing it to appear in a different location than its true one, a serious risk in narrow, crowded, or sensitive waterways. Jamming attacks can disrupt navigation or communication systems entirely, leaving vessels effectively blind and cut off from authorities.
→ Ransomware Attacks The 2017 NotPetya cyberattack crippled a global supply chain. The malware, disguised as ransomware but designed to destroy data, spread through a compromised software update and rapidly shut down major companies worldwide. While Maersk became the most visible victim, halting port and shipping operations across more than 130 countries, the attack also disrupted firms such as TNT Express, Merck and Mondelez, contributing to an estimated $10 billion in global damage.
Key Takeaways
Unified Data, Clearer Maritime Insight
Effective maritime intelligence requires cross-domain data fusion, not just more sensors. Coastal radar, UAV feeds, satellite imagery, SIGINT, SATCOM, OSINT sources (such as AIS, social media, shipping databases and government databases must be unified). When fused, these diverse data streams reveal patterns that single sensors cannot.
Context Transforms Signals into Insights
Using advanced analytics, agencies can move beyond surface-level alerts to identify suspicious anomalies, correlate vessel movements with trade flows and sanctions lists, and detect ghost fleets or illicit networks operating under cover. A drifting vessel becomes meaningful when paired with OSINT indicators, nearby dark ships, unusual AIS gaps or atypical communications activity.
This shifts agencies from reactive patrols to proactive maritime intelligence. Coast guards, navies and maritime police can detect illegal immigration routes and smuggling facilitators earlier, uncover covert ship-to-ship transfers, anticipate disruptions in strategic corridors and prioritize scarce patrol assets on the highest-risk vessels, routes and zones.
Challenge 3
Hybrid Warfare Reaches Border & Maritime Zones
Modern conflicts employ hybrid tactics that extend directly into border and maritime environments.
→ Instead of relying solely on traditional kinetic operations, states and non-state actors combine physical actions with non-kinetic methods, such as weaponized migration, cyberattacks and disinformation to weaken or destabilize adversaries without open warfare.
As these tactics expand, the boundaries between war, crime and terror are increasingly blurred. Rogue states and their proxies can use sabotage, covert operatives and attacks on critical infrastructure to advance strategic objectives while avoiding direct military confrontation.
Attacks on Critical Infrastructure and Sabotage
In recent years, several undersea energy and communications assets in Europe have been targeted or disrupted.
The 2022 Nord Stream pipelines explosions highlighted the vulnerability of offshore energy infrastructure and how physical sabotage can destabilize regional energy security. Multiple incidents involving cut or damaged undersea data cables in the Baltic Sea between 2022 and 2024. In response, NATO launched the Baltic Sentry mission in 2025, expanding maritime patrols, seabed monitoring and multi-domain reconnaissance to protect undersea infrastructure.
At the same time, several countries reported drones probing offshore platforms, including North Sea energy installations. This highlights the growing use of low-cost unmanned systems for reconnaissance, intimidation or sabotage.
Weaponized Migration
Hybrid tactics also include the deliberate manipulation of migration flows to exert political pressure. Recent incidents illustrate how migration can be turned into a geopolitical tool that overwhelms border security of neighboring states in an effort to destabilize them:
→ 2021: Belarus allegedly facilitated the movement of thousands of migrants to EU border crossings with Poland and Lithuania, contributing to violent clashes and prolonged border standoffs.
→ 2023: Finland accused Russia of directing or enabling irregular migrant flows toward its border checkpoints, creating operational strain and prompting temporary closures.
Key Takeaways
Intelligence remains fragmented across agencies
Hybrid threats exploit gaps between teams within a single organization, as well as among government organizations that need to work together. Critical data from cyber signals to maritime movements stays siloed, limiting early detection and coordinated response.
Unified, multi-source intelligence is required to reveal cross-domain activity
Data fusion and advanced analytical capabilities are needed to correlate multi-source intelligence, highlight cross-sensor patterns and prioritize points of interest, giving military, intelligence, law enforcement and border units a shared operational picture for quicker, more effective decisions.
Challenge 4
Irregular Migration On A Mass Scale
Large and unpredictable migration flows are placing unprecedented strain on border security. Illegal migration is accelerating due to a convergence of violent conflicts, regime instability, climate stress, economic collapse and social media disinformation amplified by smuggling networks.
Criminal groups and state-backed actors increasingly exploit these vulnerable populations, using migration routes as cover for smuggling, trafficking and covert movement. Smuggling networks now weaponize connectivity, coordinating operations through encrypted messaging apps, spreading videos promising "guaranteed routes," using satellite internet to avoid detection and enabling payments through cryptocurrency, making their operations harder to detect and disrupt.
Regional Examples
Balkan Route into the EU
The Balkan corridor remains a major gateway for migrants moving from the Middle East, Central Asia and Africa into the EU. Flows shift frequently due to political changes, seasonal conditions and varying border controls. Smuggling networks coordinate movement through remote terrain, provide forged documents and exploit gaps in land border monitoring.
Mediterranean and North Africa Routes into the EU
Mediterranean routes continue to see high volumes of irregular migration departing from North Africa and coastal hubs. Smugglers coordinate departures to exploit weather and patrol gaps, and increasingly rely on satellite phones, GPS devices and online recruitment to smuggle people into southern Europe.
Central and South American Corridors
South and Central America encompass multilayered land and maritime routes used by migrants from across the region and beyond in their attempts to reach the US. Criminal groups control key transit stages. They extort the vulnerable migrants for paid passage and protection services while coordinating these movements migrants through encrypted messaging and alternative financial channels like prepaid debit cards, cryptocurrencies or digital wallets.
Key Takeaways
Managing large and fast-moving migration flows requires agencies to see far beyond the physical border. Border intelligence enables early detection of intent, organizers, emerging routes and high-risk subgroups by fusing multi-domain data into one coherent picture.
Understanding Intent and Organizers
Border intelligence can help authorities analyze communications, social media activity and financial indicators to distinguish humanitarian movement from coerced or illegal migration. Pattern-of-life analysis and behavioral profiling help zero in on traffickers, smugglers or criminal infiltrators within larger groups, while ensuring vulnerable populations receive appropriate protection.
Anticipating Shifting Routes
Imagery and geospatial analytics can help authorities identify emerging routes, and AI forecasting enables agencies to anticipate pressure points and respond proactively.
Cooperation and Intel Reduces Risks
Recent data show that irregular crossings along the Balkan route fell by more than 50% in 2025, reflecting stronger controls and regional coordination. Sustaining these gains requires continued close cooperation between countries and agencies, supported by shared intelligence and coordinated action to detect routes and prevent renewed surges.
Challenge 5
Cross-Border Crime On An Industrial Scale
Transnational criminal networks now operate with the sophistication of multinational supply chains, moving drugs, weapons, people and illicit goods. They exploit jurisdictional seams between border agencies, navies, customs, intelligence units and financial regulators, shifting routes quickly and blending into civilian environments to avoid detection.
These groups increasingly leverage advanced technologies to expand their reach and evade detection. They rely on encrypted communications, satellite broadband, submersibles, commercial drones, cryptocurrencies and dark web coordination. Some deploy military-grade weapons, hardened vessels or covert sensors, making apprehension difficult.
Social Media & Messaging Apps
Smuggling networks use encrypted apps and social platforms to recruit migrants, advertise routes and coordinate movement anonymously.
Cryptocurrencies
Criminal groups use cryptocurrencies to move and launder profits quickly and anonymously, making financial tracking significantly harder.
Satellite Broadband
Next-generation satellite internet (such as Starlink) enables high-speed communication in remote regions, helping criminal groups bypass national telecom networks.
Narco Subs
Cartels operate stealthy semi-submersibles that evade detection while transporting large quantities of narcotics over long distances.
Drones
Low-cost drones give criminals an aerial advantage for reconnaissance, smuggling and weaponized activity across land and maritime zones.
Autonomous Smuggling
Criminal networks are beginning to deploy autonomous vessels and vehicles to move illicit cargo with minimal human presence, reducing risk and detection.
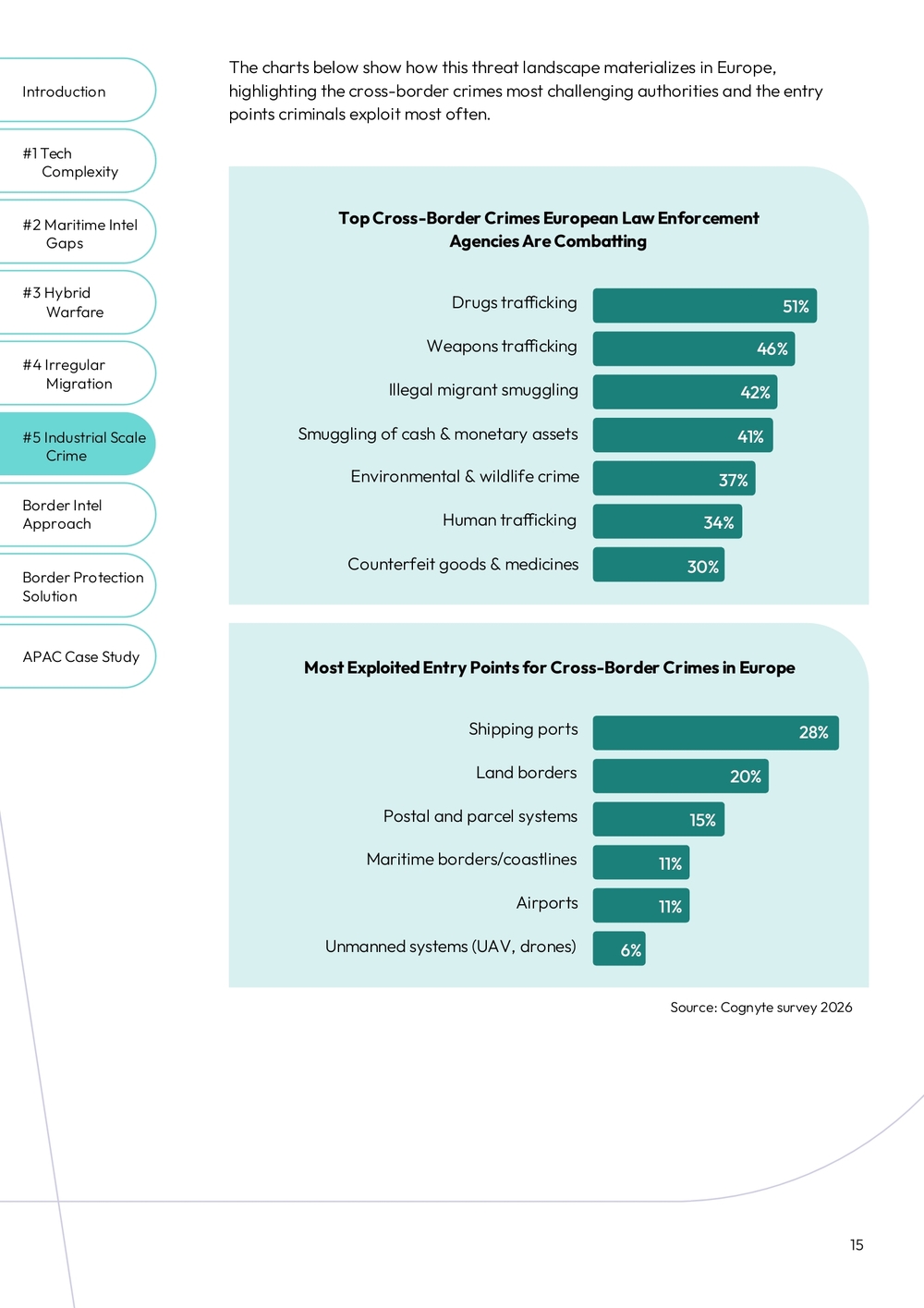
Top Cross-Border Crimes European Law Enforcement Agencies Are Combatting
- Drugs trafficking: 51%
- Weapons trafficking: 46%
- Illegal migrant smuggling: 42%
- Smuggling of cash & monetary assets: 41%
- Environmental & wildlife crime: 37%
- Human trafficking: 34%
- Counterfeit goods & medicines: 30%
Most Exploited Entry Points for Cross-Border Crimes in Europe
- Shipping ports: 28%
- Land borders: 20%
- Postal and parcel systems: 15%
- Maritime borders/coastlines: 11%
- Airports: 11%
- Unmanned systems (UAV, drones): 6%
Source: Cognyte survey 2026
Key Takeaways
Technology Enables Criminal Agility at Scale
These technologies create an asymmetry which allows relatively small criminal organizations to operate globally and outmaneuver slower, compartmentalized government organizations. For security forces, this means confronting agile, tech-enabled adversaries capable of exploiting every gap in monitoring networks, intelligence sharing and operational coordination.
Global Crime Requires Shared Intelligence
Today's criminal networks scale globally because they exploit the gaps between agencies, jurisdictions and intelligence systems. No single country can confront these criminal networks alone. Multinational collaboration among agencies are essential to share timely intelligence, track dual-use technologies and enforce global compliance standards.
Cognyte's Border Intelligence Approach
Modern border threats span physical, digital and informational domains, making single-source intelligence insufficient. A modern border intelligence approach enables correlating SIGINT, OSINT, ELINT and VISINT into one coherent picture and applying advanced analytics to expose real threats, hidden patterns and operational opportunities.
Layer 1
The Sensor Layer: A Multi-Domain View
Border protection units require a complete, multi-INT perspective to uncover activity that no single sensor can detect. Each intelligence discipline contributes a unique signal; when combined, they create a complete operational picture.
- SIGINT: Analyzes communications and device activity across cellular and satellite networks
- ELINT: Analyzes electronic emissions, radar signatures and covert transmitters
- VISINT: Provides visual intelligence from drones, aircraft, satellites and fixed cameras
- OSINT: Surfaces insights from AIS, social media, shipping registries and online forums
- ADINT: Reveals device and behavior patterns via data from advertising networks
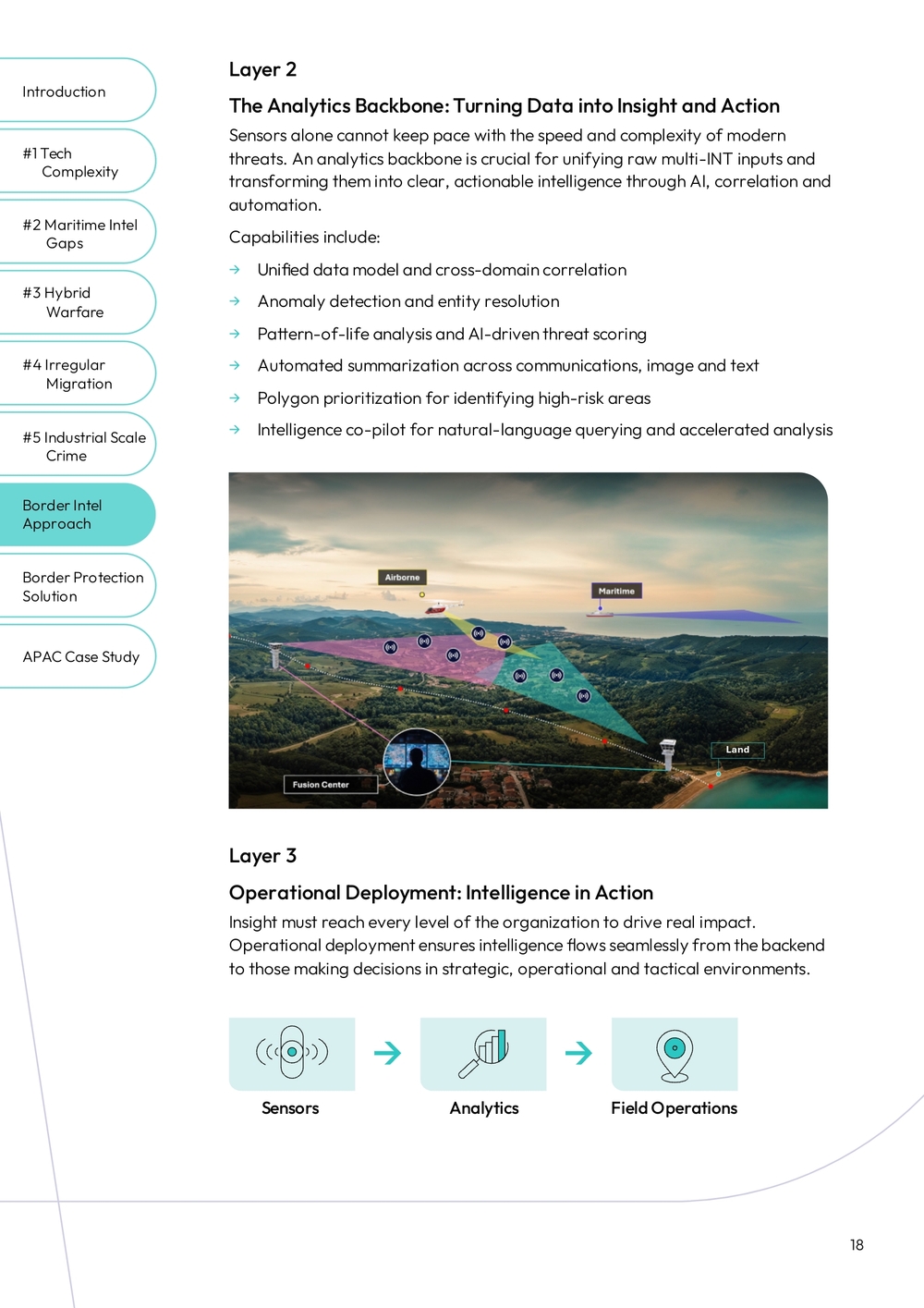
Layer 2
The Analytics Backbone: Turning Data into Insight and Action
Sensors alone cannot keep pace with the speed and complexity of modern threats. An analytics backbone is crucial for unifying raw multi-INT inputs and transforming them into clear, actionable intelligence through AI, correlation and automation.
Capabilities include:
- Unified data model and cross-domain correlation
- Anomaly detection and entity resolution
- Pattern-of-life analysis and AI-driven threat scoring
- Automated summarization across communications, image and text
- Polygon prioritization for identifying high-risk areas
- Intelligence co-pilot for natural-language querying and accelerated analysis
Layer 3
Operational Deployment: Intelligence in Action
Insight must reach every level of the organization to drive real impact. Operational deployment ensures intelligence flows seamlessly from the backend to those making decisions in strategic, operational and tactical environments.
Sensors → Analytics → Field Operations
Cognyte's Border Protection Solution
With more than 30 years of operational expertise, Cognyte understands that border protection is ultimately a race against time. By the time a threat reaches the border, the opportunity to prevent harm is often lost. Cognyte's Border Protection solution gives security forces the advantage by combining advanced field sensors with a powerful analytics backbone to detect and deter threats before they reach their borders.
Our solution integrates with all existing sensors and data sources which border forces have access to, as well as delivering powerful new capabilities.
Multi-Domain Tactical Intelligence Capabilities: Air, Land and Sea
Cognyte's tactical intelligence solutions provide border forces with a borderless view of activity across air, land and sea, including remote areas and rough terrain.
Decision Intelligence Platform
At the heart of the solution is NEXYTE, Cognyte's AI-powered analytical backend. NEXYTE fuses SIGINT, VISINT, ELINT and OSINT into a unified intelligence picture, and leverages advanced analytics and AI to expose anomalies, detect early indicators of illicit behavior.
End-to-End Intelligence, From Detection to Engagement
Cognyte supports the full operational cycle from wide-area reconnaissance to precise target engagement. Our solution integrates land, maritime and airborne intelligence, delivering one trusted view that helps teams act decisively and in sync.
This intelligence-driven approach enables agencies to:
- Anticipate threats earlier
- Deploy resources more efficiently
- Reduce false positives
- Accelerate operational decisions
- Coordinate responses across units and command levels
Cognyte empowers border forces to shift from reaction to prevention with the intelligence advantage needed to stay ahead of evolving threats
Case Study
APAC Maritime Intelligence Success
A national maritime enforcement agency in the Asia-Pacific region sought to counter growing illicit maritime activity, including covert fuel transfers and sanction evasion operations.
Using Cognyte's Border Protection solution, the agency:
- Integrated AIS feeds with SIGINT, satellite imagery and behavioral analytics.
- Detected a cluster of fishing vessels performing concealed nighttime ship-to-ship transfers.
- Identified vessel identity manipulation and irregular communication signatures.
- Mapped the network's pattern-of-life across multiple maritime corridors.
- Supported successful interdiction operations that disrupted the fleet's ability to operate.
This case demonstrates how fusing sensors for holistic situational awareness, leveraging advanced analytics and putting it into practice in the field enables agencies to transform maritime domain awareness into actionable intelligence.
Conclusion
Achieving Border Intelligence Superiority
Border protection units and maritime forces worldwide face the same fundamental challenge. Threats now, move across land, sea, air, cyber and information domains. Even when traditional monitoring tools are expanded with new towers, radars or patrol assets, they are still insufficient. Meeting this reality requires a border intelligence approach that fuses multi-domain data, surfaces suspicious indicators early and supports coordinated decision-making.
Cognyte's Border Protection solution delivers this operational advantage by unifying advanced sensors with AI-powered analytics, giving tactical teams and strategic leaders one coherent picture of evolving threats. Together, the methodology and the solution enable agencies to shift from reacting to anticipating, offering true decision intelligence superiority at the border.
Learn More
- Protect Your Borders With Precision
- Maritime Domain Awareness: Countering Hidden Threats
- The Role of Border Intelligence in Combatting Today's Border Threats
Notes
- Military experts say Baltic Defense Line is being built to be seen
- "Shield East" - an investment in peace and security
- Finland joins NATO in historic shift, Russia threatens 'counter-measures'
- AI-powered fences, drones: How Army is strengthening security along LoC
- Fear of Op Sindoor 2.0? Panicked Pakistan rushes anti-drone systems to LoC
- BBC News – Nigeria cross-border kidnapping report
- Brazil deploys Armed Forces to control airports and other key sites
- Despite Progress, Illegal Catch Continues to Reach the Market
- Hundreds of Chinese Boats Suspected of Illegal Fishing
- Sea Arrivals Overview | Europe Region | August 2025
- José Amaro, Ghost Ships & Maritime Cyber Vulnerabilities, LinkedIn
- The Untold Story of NotPetya, the Most Devastating Cyberattack in History
- The Nord Stream Incident: Open Briefing
- Could drones be a threat to offshore energy installations?
- EU accuses Belarus of 'gangster' methods as migrants shiver at Polish border
- Finland to close entire Russian border after migrant surge
- EU's external borders in 2022: Number of irregular border crossings highest since 2016
- Global Overview of Migration Routes January - April 2025
- Migration Trends in the Americas
- EU external borders: Irregular crossings down a quarter in first 4 months of 2025
- HS Today contributed article: Redefining Border Protection with a Predictive Intelligence Approach
- Cognyte Press Release: APAC Customer Enhances Border Security with Over $10M Investment in Cognyte Solutions
About Cognyte
Cognyte, a global leader in data processing and investigative analytics solutions, helps government agencies and other organizations generate Actionable Intelligence for a Safer World™. With offerings that leverage state-of-the-art technology, including artificial intelligence, big data analytics and advanced machine learning, Cognyte helps customers eliminate the unknown and make smarter, faster decisions with their data for successful outcomes.
Unauthorized use, duplication or modification of this document in whole or in part without the prior written consent of Cognyte is strictly prohibited. By providing this document, Cognyte is not making any representations regarding the correctness or completeness of its contents and reserves the right to alter this document at any time without notice.
2026 Cognyte
cognyte.com
